Fraud is the most commonly experienced crime in the UK which costs the UK many billions of pounds every year. The impact of fraud and related crime can be devastating for businesses, but today we will let you know about the most common fraud and scams we see so you can avoid them much easier.
We will talk about phishing a lot below so to start we will define what phishing is.
What is Phishing?
Phishing is the fraudulent practice of sending emails or other messages purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers or other valuable information.
Lets take a look at the top scams affecting companies below.
Change of bank details scam
This scam can start out by either your own account being phished or a supplier / customer of yours being phished which gives the scammer visibility into your email conversations.
Scammers can use phishing emails to pilfer login information and if the recipient falls for it, that can give the scammer a way in to monitor your emails by taking control of a user account. Once they do that, they may watch for an invoice being received or sent. Then they will spoof the email address of the sending company and create an identical invoice but with the scammers “new bank details” on it.
If you receive any change of bank details or you are paying an account for the first time, always telephone your customer / supplier using the telephone number you have for them and not the telephone number on the email to double check and confirm the bank details with them. This will prevent you from paying an opportunist scammer who has recently intercepted and changed bank details and other information. It only takes a few minutes but it can save you thousands of pounds!
Unpaid Invoice / Confirm bank details scam
It’s quite common to get an email supposedly from Paypal or other financial institutions to say there is a problem with your account and you risk your account being closed. A typical good example of this is an amazon or netflix email saying they will close your account if you don’t confirm your bank details. If you ever get this type of email and struggle to tell if its real, just close the email and go to the website manually via your browser. Never click links on these type of emails as it will likely take you to the fraudulent website which looks identical to the official website.
Gift card scam
We saw lots of this scam on the internet at Christmas. It is especially prevalent at that time of year as it makes it easier for scammers to execute. The scam basically starts with someone imitating a CEO or Managing Director on services like WhatsApp and they send a message to one of the employees who have their phone number on the company website. The scammer will start up a conversation asking the employee to go to the shop and buy some popular gift cards like Google Play or Apple gift cards to give to the employees as presents for all their hard work. The scammer will then make an excuse and ask the codes to be emailed to him/her as they would not be around to collect them. Once the scammer has the codes they can sell them online in exchange for real cash.
Social engineering scams
Employees should always be wary when taking calls and never assume the person on the end of the phone is who they say they are unless of course they have spoken to them previously and know them.
Scammers can trick staff into handing over confidential or sensitive information, such as passwords or bank information. It often starts with a phishing email, social media contact, or a phone call that seems to come from a trusted source, such as a supervisor or other senior employee, but creates urgency or fear. Scammers may ask employees to send money or provide access to sensitive company information. Other emails may look like routine password update requests or other automated messages but are actually attempts to steal information. Scammers also can use malware to lock organizations’ files and hold them for ransom.
Remember: If you get a random call or email from ourselves and you don’t recognise the support technician give us a call from the number on our website and we will be able to confirm or deny whose calling.
General issues to be aware of
There is a lot of spam emails going around that ask you to login to your email account and they might have a Login button. Never use those emails to login to your email account. Always use the official website or app that you’ve always previously used. Always be wary of clicking links in an email.
The common theme that runs through the scams above involve “social engineering” which is basically convincing someone that you are someone you’re not. If a scammer can convince you that they are someone else or some other official company then they don’t need any special hacking skills at that point as they may receive the information they need off you / your business / your employees.
Best way to prevent scams?
Become alert to any change of payment information, any request for information which sounds strange, or any request which is out of the ordinary especially those which are time critical. Don’t click links in emails that you were not expecting, and get a second opinion from your IT company or IT representative at your company. Check the from address on the email to make sure its exactly the correct email address if it comes from someone you may know. E.g. If you receive an email from joe.bloggs@examplecompany.com and then you get an email from joeblogs.examplecompany@gmail.com requesting a change of bank details or something then you can be sure there’s something fishy going on!
If you need us to check any messages or would like any further advice or consultancy on this please get in touch.
Regardless of the sector you operate in or the size of your business, when your operations rely on technology and access to data, it is crucial that your systems are always available and performing as required. If you have a system failure, the impact on your business can be catastrophic and can extend beyond financial consequences.
What causes downtime?
A common cause of downtime is ransomware attacks, which utilise encryption to hold the victims’ data at ransom, for a sum decided by the attacker. In the first four months of 2021, the National Cyber Security Centre handled the same number of ransomware incidents as they did in the entirety of 2020, with as many as one in three businesses being subject to cyber breaches.
A large number of businesses believe they are unlikely to be a victim of these, however a recent article from IT Pro warns that small businesses are more likely to be a victim of ransomware attacks in 2022 as cyber criminals begin utilising campaigns less likely to draw direct action from law enforcement.
Another leading cause of downtime, and one not always considered by businesses, is human error. Tech Radar details a famous example of this with the outage at British Airways in 2017. This was caused by an IT technician switching off an uninterruptable power supply, grounding 200 flights and leaving 75,000 customers stranded (Financial Times). The risk of human error causing business disruption and outages can be mitigated with proper training, but this does not eliminate the chance of it happening.
With ransomware attacks and the possibility of human error, as well as other common causes of downtime such as outdated hardware and bugs in a server’s OS, it makes sense to consider investing in solutions.
The true cost of downtime
From halting production or business operations to financial losses, data breaches and reputational damage – the true cost of downtime can be extensive.
In 2021 a study from the Phonemon Institute found the average cost of a data breach in the UK was £3.5million. However, it is important to note that it’s not just the cost of not being operational for hours or days that impact a business. One of the biggest consequences and cost factors in downtime is data loss which can cause ongoing problems for businesses.
The loss of customer and employee data can erode trust in a business and raise questions around security and GDPR. This can lead to people being less likely to use the business in the future and may make prospective employees wary of joining the company. This can affect customer loyalty and the business’s reputation in the long-term.
There are a wide range of factors that affect how much an outage will cost your business, from the amount of data on critical business systems and how regularly the data is backed up to the number of employees and business turnover.
We used a downtime calculator to estimate the cost of downtime to a business with no disaster recovery and backup solutions in place. In addition, the business has:
Data on business-critical systems: 2,500 GB
Cloud back up frequency: 12 hours
Employees: 40
Average employee salary: £25,000 pa
Average employee overhead: £10,000
Annual turnover: £500,000
It is anticipated that this business would experience more than 81 hours of downtime, costing £59,284. If the recovery process failed, it would cost the business an additional £8,700 per recovery attempt.
If the business had a disaster recovery and backup solution in place, they could have saved approximately £58,848. Recovery costs could be reduced to £1,734, and the business could be operational within 36 minutes.
Disaster recovery and backup solutions
Investing in disaster recovery and backup solutions can protect your business against substantial losses because of downtime. We provide a wide range of disaster recovery and backup solutions which can help protect your business from the impact of downtime and facilitate a speedy recovery. This includes software such as Datto SaaS Protection for Office 365 and Datto Siris.
We also offer preventative solutions such as training and cyber security software as well as ongoing IT support. Our professional IT support aims to prevent any issues before they occur, by utilising proactive monitoring software to spot faults and fix them before they escalate.
In many instances a small monthly fee for a back up and recovery solution can save a business thousands of pounds and minimise time offline. The cost of getting the right solutions and policies, far outweighs the cost in downtime – making these solutions an investment for the long term.
Find out more about the solutions we offer here.
As we kick off the new year many businesses are refreshing their business plans. But have you considered the crucial role that IT plays?
Whether your 2022 business planning starts in January, or the new financial year, it’s never too early or too late to think about how IT can support you in meeting your objectives.
We offer a range of transformative solutions which can help you meet your business objectives. This includes cloud solutions, software, cyber security, and IT support services.
Below are some examples of the many business areas and objectives our IT solutions and services can support:
- Hybrid/Remote Working – Covid-19 has accelerated, and in some instances forced, a move to remote or hybrid working. As a Microsoft Partner, we offer Microsoft 365 including Microsoft Teams – allowing you to work from anywhere and collaborate online.
- Disaster Recovery – In addition to Microsoft 365, we can help you protect the data you entrust to the cloud with Datto SaaS Protection for Office 365. A cloud-to-cloud backup product, Datto SaaS Protection offers an all-in-one backup, restore and export solution for Exchange Online, OneDrive and SharePoint Online. We provide business continuity and disaster recovery solutions at prices affordable to SMEs, so you can protect your business whatever the size.
- Business Continuity – As part of our Professional IT support, we utilise proactive monitoring software which is always analysing the performance of our customer’s system. This means that any faults are detected immediately and areas which could become an issue are resolved before our customers feel any impact. This often saves valuable time and mitigates the financial impact of any downtime or outages – supporting your business continuity.
- Increased Efficiency – We offer a range of cloud solutions and software to help you increase efficiency. This includes Draycir, a software which helps to reduce your workload by streamlining credit control and document management; Webexpenses, an award-winning cloud software for smarter expenses management; and our very own Bakery and Production Software (BaPS), which was designed to streamline and automate business management processes for bakeries, retailers, and wholesale food businesses.
- Cyber Security – Robust cyber security is essential to all businesses, and we offer a range of solutions. This includes support for Cyber Essentials, a government-backed scheme, which helps organisations defend against the most common cyber threats. In addition, many organisations, particularly those in heavily regulated sectors such as finance and defence, require those in their supply chain to demonstrate the security of their systems. Cyber Essentials can support you in evidencing and reassuring your customers that your cyber systems are secure.
Whether you are seeking to strengthen your business contingency plans, reinforce cyber security, streamline processes, improve productivity, or enhance communications – our IT solutions and services can help!
To find out how your IT software and systems can better help you achieve your business ambitions, contact our team.
Cyber Essentials advice and certification from the National Cyber Security Centre (NCSC), a part of Government Communications Head Quarters (GCHQ), helps organisations of all sizes defend against the most common cyber threats and demonstrate their commitment to cyber security.
In January 2022 the National Cyber Security Centre updated the requirements for Cyber Essentials in what is the largest overhaul of the scheme’s technical controls since its launch in 2014. The refresh of Cyber Essentials reflects, among other things, the speed of the digital transformation and the adoption of cloud services, as well as the move to home and hybrid working.
The new version of the Cyber Essentials technical requirements were released on 24 January. Any assessments already underway, or that began before that date, will continue to use the current technical standard.
Over the past 12 months we have seen a growing request for Cyber Essentials support, as the benefits of this certification are extensive. Including:
- A government-backed scheme, Cyber Essentials helps organisations defend against the most common cyber threats.
- It provides reassurance to your customers that your systems are secure.
- A Cyber Essentials certification is often a requirement for organisations working on UK government contracts.
- Many organisations, particularly those in heavily regulated sectors such as finance and defence, also require those in their supply chain to demonstrate the security of their systems.
Our experts can work with you to perform your evaluation and help you to achieve your Cyber Essentials Certificate, helping you protect your business and demonstrate security to your customers.
Get in touch to find out how we can help your business.
Source: National Cyber Security Centre – https://www.ncsc.gov.uk/information/update-to-the-cyber-essentials-technical-controls
Cyber attacks can be extremely damaging to businesses, not only by disrupting day-to-day operations, but they can also be harmful to a company’s reputation, particularly if they result in compromising client data. It is crucial that your business has reliable cyber security measures in place, from a provider you can trust, to combat cyber threats and protect your business’s operations and reputation.
What is a Cyber Attack?
A cyber attack is an assault, launched by cybercriminals, that can disable computers, steal data, or use a breached computer as a launch point for other attacks. Cyber attacks can be launched in a variety of different ways, including malware, phishing, ransomware, and denial of service, among other methods.
Almost 40% of businesses had a cyber security breach or attack in the last 12 months, as reported by The UK Government’s Cyber Security Breaches Survey 2021. Most cyber attacks are permitted by human error, by system users choosing a password that is easy to figure out or not changing the default password on devices such as routers.
What is Cyber Security?
Cyber security is the application of technologies, processes, and controls to protect systems, networks, programs, devices, and data from cyber attacks. It reduces the risks of cyber attacks and protects against the unauthorised exploitation of systems, networks and technologies.
The most effective cyber security is made up of several layers of protection, such as:
- Using multiple strong passwords
- Implementing two factor authentication
- Installing anti-virus software
- Developing a backup and disaster recovery plan
- Ensuring all employees are trained in your business’s cyber security protocol
- Ensuring all software updates and patches are completed regularly
How can we help?
Based in the North East, we provide a range of IT services and transformative technology solutions which includes cyber security, as well as cloud solutions, hardware, networking, software and IT support services, to help your business increase productivity, improve performance, enhance connectivity, and reinforce security.
We safeguard your business and mitigate the risk of cyber threats with our robust and reliable cyber security solutions. This includes Datto SIRIS Disaster Recovery and Back-Up systems, and Webroot Antivirus Protection software. Datto SIRIS is a robust business continuity solution that brings together state of the art hardware with a secure cloud storage capability. Webroot’s Antivirus Protection protects against threats across email, browsers, files, URLs, ads, apps, and more in real time. It enables endpoint management anywhere, anytime, online.
We also offer Datto SaaS cloud backup for Microsoft 365 to provide you with peace of mind and mitigate the impact of a cyber attack. Datto SaaS, a leading cloud-to-cloud backup product, protects the data you entrust to the cloud. It offers an all-in-one backup, restore and export solution that covers Exchange Online, OneDrive and SharePoint Online.
In addition, we can support you in achieving your Cyber Essentials certification from the National Cyber Security Centre (NCSC), part of Government Communications Head Quarters (GCHQ).
You can have peace of mind with Bowe Digital’s technical experts and cyber security solutions protecting your business.
Get in touch with our specialists today to find out more about how we can protect your organisation against cybercriminals here.
Our mission is to enable our customers to realise their ambitions through the provision and application of advanced technology. We offer a wide range of innovative and transformative IT solutions across the North-East to help your business increase productivity, improve performance, enhance connectivity, and reinforce security. This includes IT support, cyber security solutions, software, cloud systems and more.
Below are just some of the many services and software we offer.
IT Solutions
We understand IT systems are crucial to the running of your business, so we offer two IT support packages based on your needs. Both our IT Support Standard and IT Support Professional offer an audit of your network and infrastructure, phone and remote dial in support, webinar and seminar invitations, managed updates for servers and computers and more. Our Professional IT Support package offers onsite support, as well as Webroot antivirus protection, quarterly reports and proactive IT monitoring, to keep your systems running smoothly.
Microsoft 365 Installation and Migration
We offer Microsoft 365 Installation and Migration, which allows you to share and create anywhere, on any device, by combining best-in-class apps like Excel and Outlook with powerful cloud services like OneDrive and Microsoft Teams.
Cyber Security
We can help you to protect the data you entrust to the cloud with Datto SaaS Protection for Office 365, a leading cloud-to-cloud backup product offering an all-in-one backup, restore and export solution that covers Exchange Online, OneDrive and SharePoint Online. We work in partnership with Datto to provide business continuity and disaster recovery solutions at a price affordable to SMEs, so you can protect your business whatever the size.
We also offer antivirus protection with Webroot, which provides endpoint protection that secures your business by harnessing machine learning, classifying, and scoring 95% of the internet three times a day, to keep your information safe.
Certifications
Protect your organisation against cyber-attacks and demonstrate your commitment to cyber security with advice and certification from the National Cyber Security Centre (NCSC), part of Government Communications Head Quarters (GCHQ). We can support you in achieving your certification.
VoIP
Also known as Hosted Telephony, VoIP refers to the idea of making calls over the internet as data rather than a traditional analogue phone system, which can significantly reduce call costs particularly when making international calls.
VoIP allows users to make international calls without the expensive rates non-VoIP users receive. With calls moving as data, a business using Packnet would be able to get free calls between employees in different countries. Calling VoIP-to-VoIP is becoming the more cost-effective option with straightforward charges as VoIP users do not have to rely on a fixed monthly fee.
Training
Training is an integral part of the service which we offer. We include training in all new business proposals to ensure that the end user feels comfortable using their chosen product to its full potential. We also provide expert training on all our software products including BaPS and Microsoft.
Hardware
We have extensive knowledge and a breadth of experience to draw on when choosing the best hardware for your business. We can also advise you on which new hardware will work best with your current equipment, saving you time and money.
To find out more about how we can help your business with our extensive IT solutions and services, contact us here.
What is Multi-factor Authentication (MFA)?
Multi-factor Authentication (MFA) is a security system in which to gain access to a specific resource you need to provide two or more forms of identification. Some examples of this may be entering your password in addition to either a pin code sent to your mobile device, an authentication app, a fingerprint or a security key.
The majority of security breaches are due to insecure passwords. MFA helps prevent this as with a username and password alone, an attacker will not be able to gain access to a secure system or resource. This is because although they may have compromised the username and password, they still lack the second factor required to gain access.
So why implement Multi-factor Authentication (MFA)?
- According to Microsoft, when you implement MFA your accounts are up to 99.9% less likely to be compromised
- Implementing MFA can be low cost, or even free, depending which service(s) you use
- MFA can give you peace of mind that your data is secure when being accessed from locations other than the office
- MFA is generally very easy to use
- Small businesses are increasingly being targeted by cyber criminals. MFA makes it much harder for them and is easily rolled out
- Users are already becoming accustomed to using MFA for things like online banking
MFA is highly recommended by IT Security professionals:
- Alex Weinert, Microsoft’s Group Program Manager for Identity Security and Protection says, “Your password (rules) don’t matter, but MFA does. Go turn on MFA if you haven’t.”
- Symantec have said that 80% of security breaches could be prevented by using MFA
- The National Centre for Cyber Security (NCSC) in the UK recommend the use of MFA
- We at Bowe Digital use MFA in order to access Microsoft 365, Webroot, our RMM service and more
In conclusion, implementing MFA is definitely a step you should take in order to protect your business. The benefits of implementing MFA outweigh the drawbacks and it is an easy way to improve your security.
Contact us today for advice on how you can enforce MFA and protect your company.
Phishing is a form of cyber attack where attackers attempt to trick users into doing ‘the wrong thing’, such as clicking a bad link that will download malware, or direct you to a website which may look identical to the original website, but may harbour spyware or be designed to collect your personal or financial information. In 2018 alone, phishing was responsible for $48,241,748 (£37,232,981.11) in losses.
Phishing can be conducted via a text message, social media, or by phone, but the term ‘phishing’ is mainly used to describe attacks that arrive by email. Phishing emails can reach millions of users directly, and hide amongst the huge number of benign emails that busy users receive. Attacks can install malware (such as ransomware), sabotage systems, or steal intellectual property and money.
Phishing emails can hit an organisation of any size and type. You might get caught up in a mass campaign (where the attacker is just looking to collect some new passwords or make some easy money), or it could be the first step in a targeted attack against your company, where the aim could be something much more specific, like the theft of sensitive data. In a targeted campaign, the attacker may use information about your employees or company to make their messages even more persuasive and realistic. This is usually referred to as spear phishing.
What does a Phishing email look like?

In this example above, we can see an email purporting to be from OneDrive, advising that there is a file which has been sent through to the user. Clicking the link in this email will result in malware being installed on your system. This is a common method of phishing where the attacker creates a message which would not look out of place amongst your normal work emails.
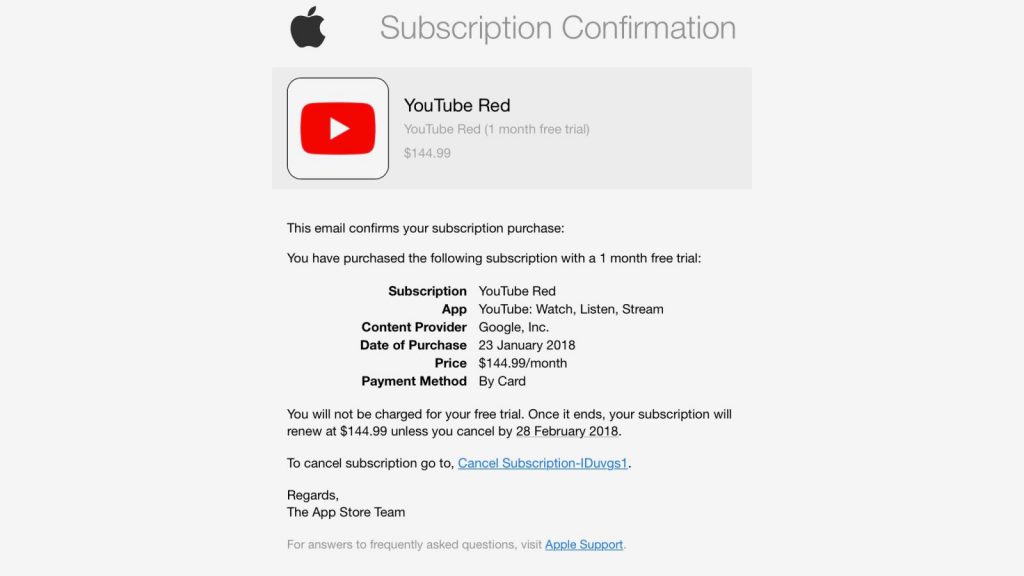
In this example above, we can see that an attacker has sent out an email attempting to get users to click the link and enter their Apple ID credentials. This may look convincing upon first glance, but as we look into it further, we can see that it is clearly not a genuine email. The combination of a non-apple email address being used to deliver the message, a generic and non-personalised greeting and the link pointing to a destination which has nothing to do with Apple are clear giveaways.
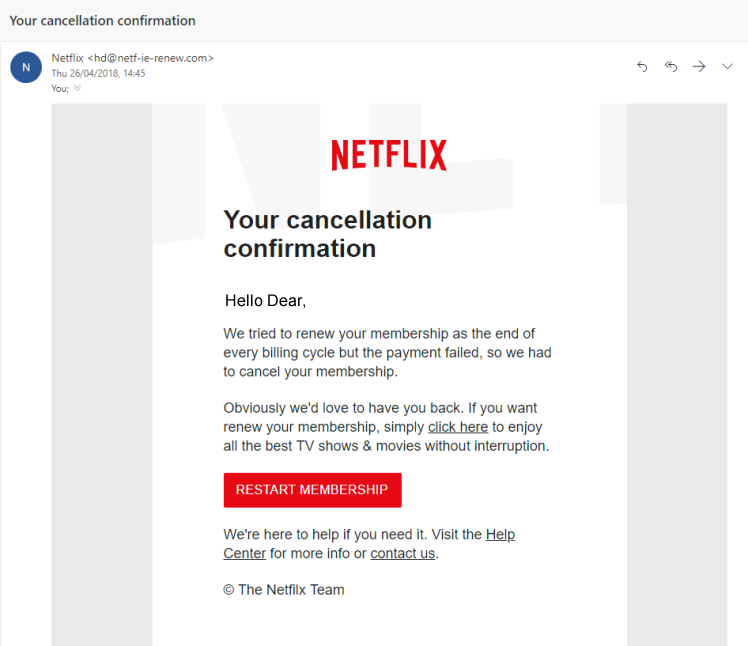
This example is one of the most common variants of a phishing email. On the surface, it looks pretty convincing – the branding is correct, the sign off seems correct and the look of the email seems legitimate apart from the recipient’s name. The only way you would be able to tell that this is not a legitimate email is to check the link in the email by hovering over it. In this case, it brings you to a false logon screen which is designed to steal your password. Another giveaway can be the email address that the message has originated from. Unless it is an @netflix.com (NOT @mailer.netflix.com or similar) email address, chances are it’s a phishing attempt.
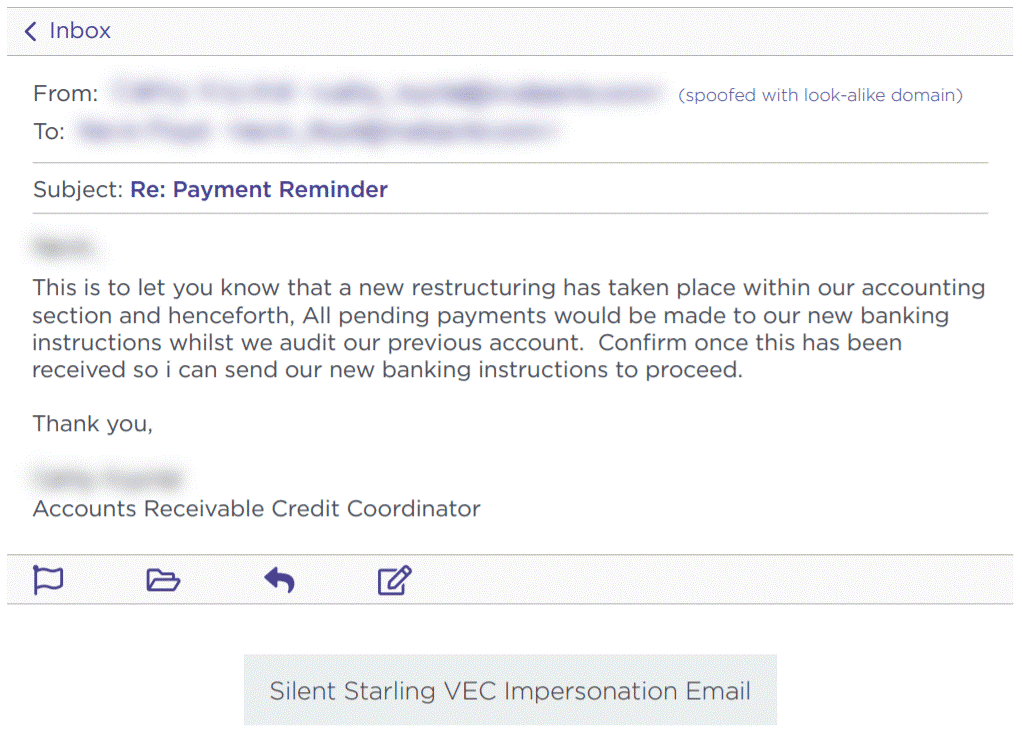
Another common type of phishing email is what is commonly known as ‘change of bank details fraud’ or ‘invoice fraud’. This involves a fraudster posing as a member of the accounts department of a supplier. The fraudster creates a convincing looking email and advises that their bank details have changed with the aim of getting you to make payments to the new account.
In order to avoid scams such as this, it is essential that you work on a basis of distrust when it comes to financial matters. If you are contacted out of the blue by a supplier to advise that their bank details have changed, call the customer on their official number (not the number in the email) and confirm this. If you receive an invoice that doesn’t seem quite right or that comes from a different email address, call the customer and check. It is better to be overly cautious than reckless – especially when bank details are involved.
So how can we avoid becoming a victim of these sorts of attacks?
Firstly, we suggest treating every email with a degree of suspicion. Think about the following:
- Is the sender’s email address correct? Often attackers use similar email addresses to legitimate senders so it is best to check this very carefully
- Were you expecting this message?
- Are there any ‘red flags’ such as spelling mistakes, incorrect information or suspicious attachments?
- Is there a request for payment or for you to sign in using your password?
- Does the message have a threatening tone? For example, does it advise that unless you take action immediately there will be severe consequences?
- Do you use the product which is mentioned?
- Is the email from someone you know and communicate with regularly?
When in doubt, it is always better to be safe than sorry. If the email purports to be from someone you know, call them and check that it is a legitimate message. If it appears to be from your bank or a government department, call them on the correct number and confirm (NOT the number in the email you have received, but the number from their official website).
Follow us to keep updated with all the latest IT news, tips, tricks and best practices.
References:
https://www.ncsc.gov.uk/guidance/phishing
https://it.sheridancollege.ca/service-catalogue/security/images/phishing-samples/amazon-phish.jpg
https://resources.infosecinstitute.com/category/enterprise/phishing/#gref
https://heimdalsecurity.com/blog/vendor-email-compromise-vec/
Header image credit – https://www.freepik.com
As a business, IT security should be your primary concern. Although passwords have been around since 1961, they can be one of the first steps in keeping your business safe but can often be the weakest link.
Password Policies and Procedures
Having a standard policy for passwords – e.g. Minimum character count, at least 1 capital letter, 1 number and 1 symbol – is a good start to improve this typically weak area.
All of this however will be inevitably in vain if you, as a company, do not have proper procedure in place to follow regarding passwords.
This could include for example:
- Not disclosing your password.
- Not leaving your password written on a document left lying around the office.
- Not left cached inside browser windows.
Having a set procedure in place for your staff to follow can be crucial in making sure your business stays safe and secure.
The impact of non-secure passwords
A weak or non-secure password can cause a plethora of issues for you as a business.
Your password is the key to accessing your accounts and your systems, especially on the cloud, which means a weak password is like leaving the key in a lock. Having the same password for multiple accounts across your business can be likened to that same key being able to open all the other doors.
Once those doors are open your business is vulnerable, this could be in the form of ransomware or data theft or a whole host of other issues that could plague your business.
These threats could cause business downtime leading to a loss of time and money whilst you try to fix the problem and recover from it, not to mention GDPR.
Password Managing Applications
A password manager is an application that both generates secure passwords and stores those passwords to be used later. All you need is to remember your 1 master password to access the application.
Advantages of these are:
- You only need to remember one secure password.
- You can then use large strong generated unmemorable passwords for every other service, as you don’t need to remember those.
- They can be auto filled to your website login boxes so you don’t even have to type them in making logins to websites almost immediate.
- Works across multiple devices. The phone APP and chrome browser extension work in tandem, so your passwords are all with you, wherever you go.
As an extra layer of security, you should turn on two factor authentication (2FA) which we will cover later. This would mean that to access your password management software you would need a code generated on your mobile phone app typically google authenticator or a variant of that to login.
What we recommend
Here at Bowe, we recommend our businesses follow a standard business procedure for passwords.
This standard procedure involves:
- Changing passwords at every agreed interval – 30 days recommended
- Having a minimum of 8 characters to a password, at least 2 numbers and including at least 1 special character within the password.
We encourage this to try and make sure all our partners are as secure as they can be and limit the risk of potential threats to their business.
If in doubt you can check your password on https://www.haveibeenpwned.com/passwords to see if your password is on a password breach list of approximately 555 million passwords. If it is, change it immediately. Password breach lists are used by hackers to attempt access to accounts. The is serviced by https and is ran by trusted security researcher Troy Hunt.
Two factor Authentication
Anytime two factor authentication is available we recommend you set it up. It is worth noting two factor authentication through SMS is not as secure as google authenticator 2FA due to the possibility of a sim swap attack. This involves someone persuading your mobile phone carrier to swap your mobile number to their new number with a story that they have got a new phone. If they can convince the mobile phone carrier to change it, or by answering the security questions correctly, then your two factor codes will go to the attacker allowing them to reset your password and gain access to your accounts.
For the highest security two factor authentication, we recommend using a Yubikey. These are USB devices which have a button on them for you to press when generating a code.
Biometric Authentication
You will have heard of Face ID and finger print scanning. These are a way of proving that you are you. These are a great way of adding additional layers of security if the option is available to the system.
Summary
There are many ways in this day and age to protect your online accounts from hackers and a multi layered approach is always best. If there are ways of adding extra security so you are not just relying on a password to gain access to systems, then those should be investigated.
Top Image Credit: Technology vector created by slidesgo – www.freepik.com
If the recent global ransomware attack taught us anything, it is that everyone needs to be vigilant when it comes to cyber-security.
Among those issuing warnings was the Federation of Small Businesses (FSB) who urged business people not to make the mistake of assuming only big business is at risk.
The federation is warning small businesses in the UK to take urgent steps to protect themselves.
Dave Stallon, commercial director at FSB, said: “We are raising the alarm with the UK’s 5.5 million-strong small business community. It is vital that small businesses and the self-employed prioritise this and that they do it today.”
We agree. In addition to offering a range of IT solutions that can help businesses take advantage of the digital revolution, Bowe Digital can also advise on your cyber security.
Call us on 0191 214 1750 or email info@bowe.co.uk to find out how.
Bowe Digital – we make I.T. happen